Quantitative Risk Management with FAIR — Stage 1 — Ransomware scenario
Quantitative Risk Management with FAIR — Stage 1 — Ransomware scenario
In order to perform the risk analysis, we’ll need to work with some assumptions so it’s key that those are clear and documented, so they can be improved and challenged by those involved and that usually means both risk analysts, engineers and business owners.
So for this example, I’ll be analysing a Ransomware scenario to the Juice Shop organisation and you can see a graphical version of the assumptions for the scenario in the Wardley Map below, created with MapScript
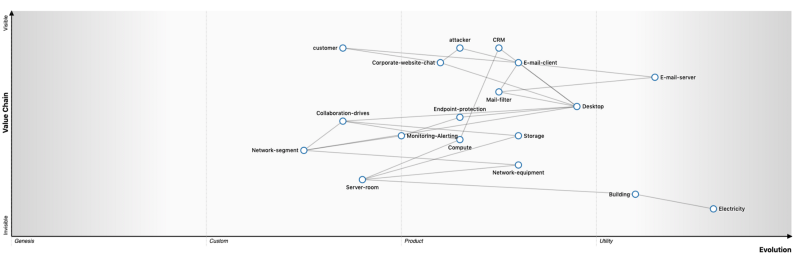
The actual map can be accessed as https://tinyurl.com/y4rb5u66
For this scenario, we’re using FAIR to assess the risk of our organisation being affected by a Ransomware attack, and for that we’re analysing a few different vectors (not all, for instance we’re excluding drive-by or ‘malvertising’) but focusing on infections through user-initiated actions like clicking a malicious link in an email and/or visiting a malicious website through clicking the Corporate Chat platform or through CRM information.
Identifying scenario components
From the scenario, we can also assume that we have a team of Contact Centre staff which is located in a central building, and the IT Compute platforms used are hosted in a Server Room in that same building apart from the Email-server which is a SaaS service offering, like O365 Exchange. The Desktop machines used by staff are Windows 10, connected to the local network which has only limited network segmentation and have a general purpose Anti-virus product installed without any particularly advanced features (like advanced containment or behavioural analysis) and mostly relying on signature-based detection. Another relevant security control is the mail filter that is associated with the SaaS email service, but only a basic licence has been procured without any advanced threat detection features. Staff use Microsoft Outlook as e-mail client.
The alerting and monitoring is done by the local IT staff (2 engineers) but no effective correlation and performed from the console of the product.
Identifying the asset at risk
This is a crucial stage of the risk analysis, as the better we can describe what we’re concerned with, the more targeted and relevant our analysis is going to be. We could make the assessment focus on the Desktop machines, with the rationale that the threat could materialise in this scenario through actions performed by staff on the Desktop computers.
However, in a ransomware scenario, what we’re really concerned with is not the loss of productivity or data on a single desktop device which expectedly the organisation impact would be low, but in ‘Corporate data’ that the Desktop has access to, as typically Ransomware attacks will encrypt all the data that is mounted in it (local storage plus any file-servers to which it may have permissions for), plus we’re also going to be assuming that this Ransomware will attempt to infect other machines on the same network segment as that’s an often seen behaviour making the attack even more devastating and business impacting.
Identifying the threat community
The final step in Stage 1, is to identify who we’re protecting against so the threat community. Depending on the scenario we could have internal threat communities like employees, contractors, vendors and/or partners, or we can have external threat communities like individual cyber criminals, organised groups, nation-states, activists, non-professional hackers.
For this scenario, we’ll focus on individual cyber criminals and organised groups as the scenario assumes Juice Shop could become the target of specific Ransomware campaigns which would typically be performed by these groups, so it explicitly excludes spear-phishing or targeted attacks against the organisation.
Conclusion
This then concludes Stage 1 of a FAIR Risk assessment. We have clearly defined the components and scope of what is under assessment, and particularly called out what are the exclusions to the scenario. We’ve identified all components that can take a part in influencing the assessment, we’ve identified the assets under assessment and finally the threat community we want to assess against.
These will now serve as the requisites for performing Stage 2 of the analysis (which I may break into multiple blog posts due to the size and because I want to clearly articulate all assumptions and thought process behind them), so that hopefully I can be challenged on them and improve the overall quality of it.
Until next time,
Mario Platt
NEXT IN SERIES→ https://medium.com/@marioplatt/quantitative-risk-management-with-fair-evaluate-loss-event-frequency-395d31eba908