Chinese Strategic Thinking and Cyber Security: Remaining Flexible
Chinese Strategic Thinking and Cyber Security: Remaining Flexible
One really important concept for me, is that of avoiding fixed responses or “one-size-fits-all” approaches in most things we do in Cyber Security.
A key aspect to that effect is to ensure we appreciate the nature of each of the problems we’re facing and that we apply the appropriate methods to deal with them.
I personally like to see this in 2 different dimensions:
- Level at which it is dealt with
- Rigidity of approach at each level
Level at which it is dealt with
Derek M C Yuen mentions that “… one should never focus on just one spot in the overall strategic picture. If a problem cannot be resolved at one level, there are always other means available at the levels of war above — operational, diplomatic, political, economic, and even psychological.[] This finally leads to Sun Tzu’s ultimate teaching of war: “Subjugating the enemy’s army without fighting is the true pinnacle of excellence”
When we discuss Cyber Security with our Executive teams or Boards, are we as an industry considering these different levels ? I will deliberately not try and provide answers for the application, as I believe the true strength of these is in asking the questions and the insights it can provide. Some questions may be:
- Within our organisations, how are we positioning our messages and plans at the diplomatic and political levels ? Are we just waving the “fines wand” to get traction ?
- At the economic level, are we finding solutions that will address threats at a price point which can be afforded ? Are we creating enough barriers or strategic thinking into our control environments such that it’s economically expensive for our attackers to target us as opposed to our competition ?
- At the psychological level, are we unveiling the personal objectives of our Executives or Boards and mapping to our security objectives so there’s clear line of sight between them ? Do we have enough deterrents and misinformation so that our attackers have a hard time understanding our true form ?
Thus although you are capable, display incapability to them. When committed to employing your forces, feign inactivity. When your objective is nearby, make it appear as distant; when far away, create the illusion of being nearby. Sun Tzu
Most Cyber Security professionals have dismissed “Security through obscurity” as a not an honorable way of doing security, but as Duke Hsiang of Sung (I’ll discuss this story in future blog posts) learnt the hard way, exposing your true form is likely to lead to your demise.
No, a gentleman should never attack one who is unprepared
Our Cyber adversaries will NOT wait for us to prepare ourselves.
Choosing the appropriate level at which to address our concerns is key to being both effective and efficient.
Rigidity of approach at each level
The Rigidity of our approaches have a number of implications at different levels. On one hand, though we should aim to have Playbooks to deal with common scenarios, that is not enough to provide assurances that we’ll deal with incidents or situations successfully, as when the conditions for the application of those playbooks change we a) may treat a complex problem like it’s linear and ordered which will lead to failure or b) have no effective methods to deal with the incident or situation at hand and thus compromise our objectivity when in “the heat of the moment”
This is where I believe the West has done great strides in developing frameworks to help with decision making in uncertainty.
A particular approach that is currently under development by Brian Rivera is combining Cynefin framework with the OODA loop, developed by John Boyd and influenced by both Sun Tzu and early Complexity thinking.
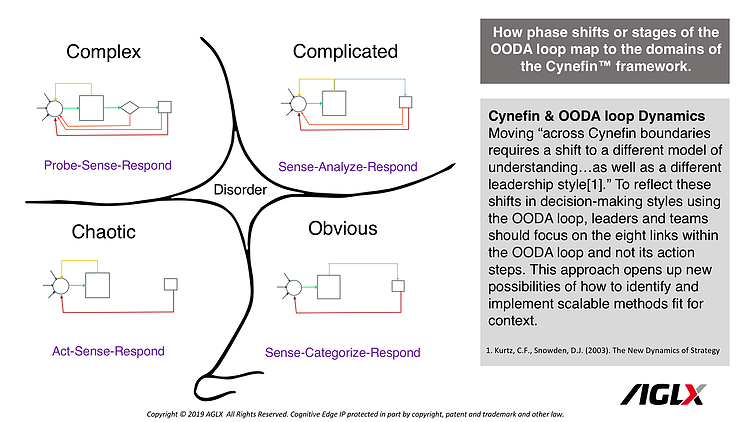
Understanding the nature of the problem we’re dealing is absolutely critical to ensure we apply the appropriate response and that we define success in a way that is coherent with the problem space we’re in. But this requires a great appreciation of the problem space as well as of options that may be available to us. Over the coming months I’ll be trying to explore this diagram further in its application to Cyber Security.
To me, this clearly illustrates that the space of playbooks/processes and slightly more rigid approaches like Compliance frameworks and Gartner-infused control selections have their application on the right hand side of Cynefin (ordered systems) which can be Obvious (security “common sense”) or Complicated (the domain of experts). But they will be wholly inadequate to deal with Complex problems nor would they likely provide us the insight to inform decision making in the Complex space. We’ll need different approaches.
For us in Cyber Security, this should be a great reminder that “AI-all-the-things” and “encryption-everywhere” or even “agile-it”are interesting and modern memes, but aren’t necessarily Strategy. You need much more Situational Awareness than that in order to create a coherent approach that is holistic and can be helpful when dealing with any type of problem space
Conclusion
This leads me to the notion of absolute flexibility (quan bian), which doesn’t have just this implication or scope I’m about to quote but also deals with of effecting restraint in responses.
“[] the nature of conflict requires an ability to transcend fixed responses to particular contingencies. Quan bian in effect states that when facing a contingency, choose any and all actions that will achieve one’s goals. One could argue, then, that the essence of strategic choice in the military texts is not “not fighting and subduing the enemy” but “respond flexibly to the enemy and thus create conditions for victory” (yin die er zhi sheng)” Derek M C Yuen
As an industry, we need to stop buying into the flavours of the month and do more to improve our situational awareness as well understand the complexity of the space we operate in. Cyber Security is a very new field, we don’t have the luxury of way over 2500 years of a body of knowledge to relate to, so we’re all still finding our space.
Understanding the different levels we can operate in to help our organisations improve their security posture and also ensuring we remain absolutely flexible, using Complex adaptive system thinking to navigate the uncertainty will increase the odds of a) establishing a coherent security strategy that will yield measurable benefits and b) help us apply appropriate and flexible methods depending on the types of problem spaces we find ourselves in
Mario Platt